Free File Sharing No Sign Up: What They Still Track
You need to send a file. You find a service that says "no account needed." Great. You upload, grab the link, and move on with your day.
But "no account" is not the same thing as "no tracking." We read the privacy policies of 10 file sharing services that let you skip the sign-up form, and what we found ranged from genuinely private to surprisingly invasive.
"No sign up" means different things
There is a big gap between "no account required" and "nobody knows you were here." Some services ask for nothing at all. Others skip the account form but still collect your email, drop advertising cookies, and track your mouse movements with heatmap software.
Here is how the spectrum actually looks, ranked from most private to least:
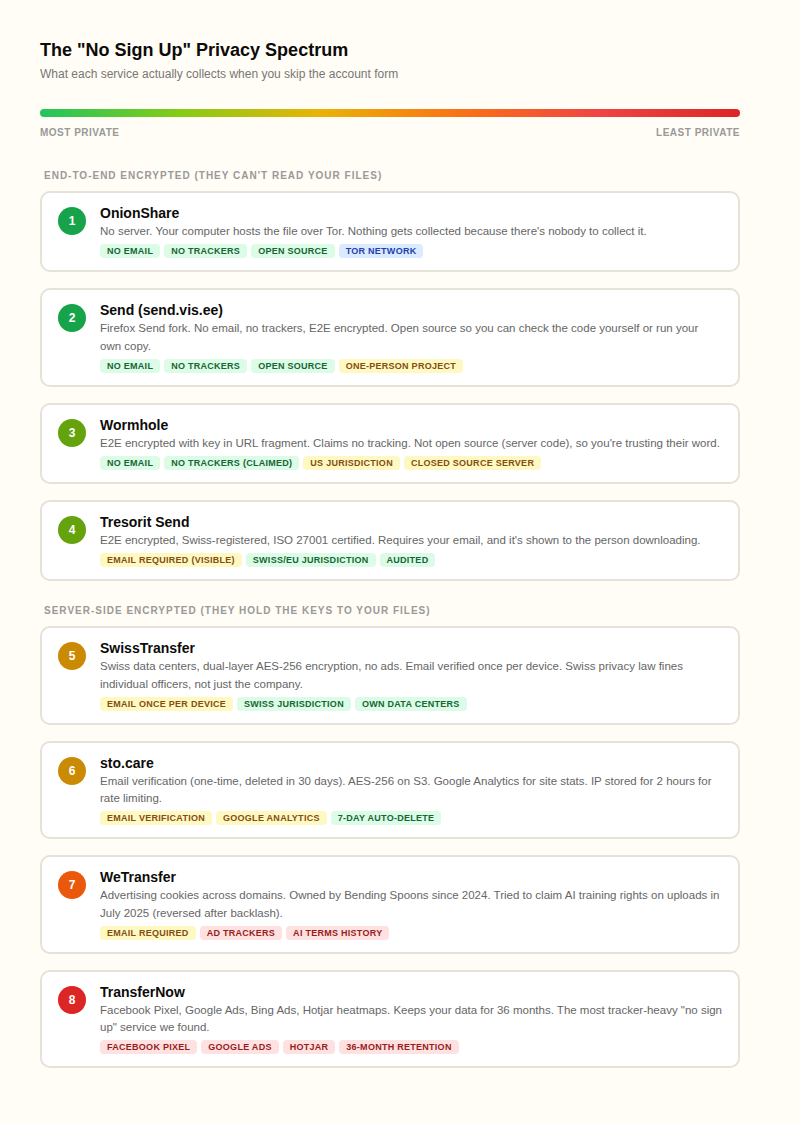
The gap between #1 and #8 is enormous. OnionShare collects literally nothing because your own computer is the server. TransferNow, on the other hand, runs Facebook Pixel, Google Ads, Bing Ads, and Hotjar heatmaps while keeping your data for three years.
Can the service read your files?
This is the question most people never think to ask. You uploaded a file to some company's server. Can someone at that company open it and look at what's inside?
The answer depends on one thing: where the encryption key lives.
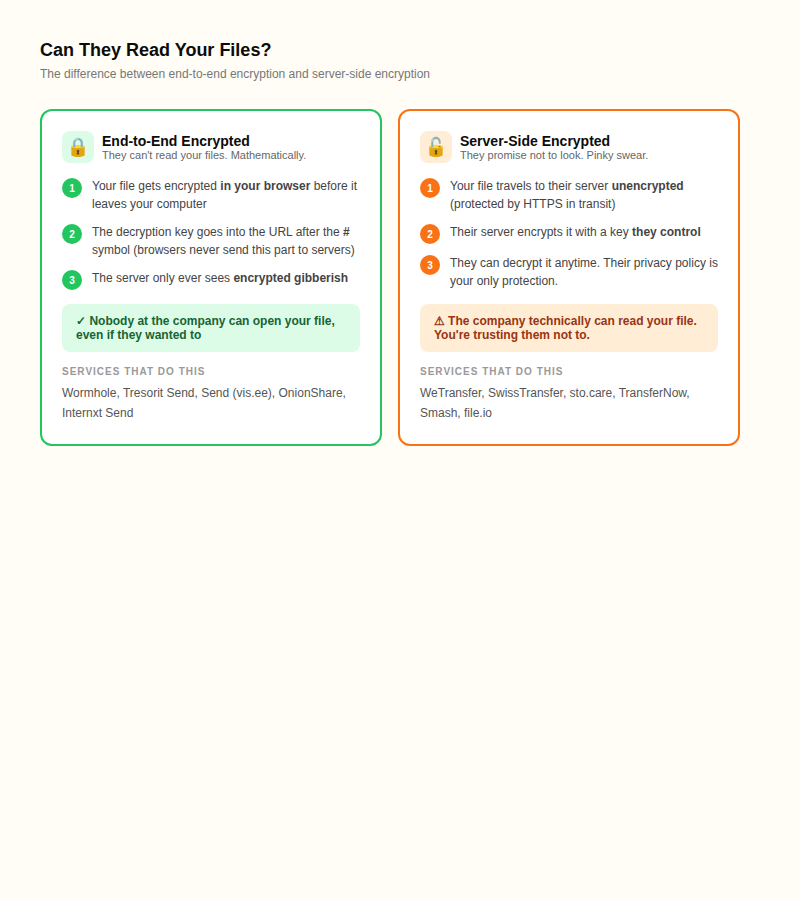
With end-to-end encryption, your file gets scrambled in your browser before it ever leaves your computer. The key that unscrambles it goes into the URL after the # symbol. Browsers never send that part to any server. So the company only ever sees encrypted noise. They could not read your file even if a court ordered them to.
With server-side encryption, your file travels to their server, and then the server encrypts it with a key the company controls. This protects against someone breaking into the storage drives, but the company itself can decrypt your file anytime they want. Your only protection is their privacy policy.
Wormhole, Tresorit Send, Send, and OnionShare use end-to-end encryption. SwissTransfer, sto.care, WeTransfer, and most others use server-side. We built sto.care, so we are being upfront: we use AES-256 encryption on S3, and we hold the keys. We cannot read your files without going out of our way to do so, but technically we could.
What is actually tracking you?
We checked the privacy policies and cookie disclosures for each service. The differences were stark.

A few things stood out. TransferNow is the most tracker-heavy service we found. Facebook Pixel means Meta knows you uploaded a file. Google Ads means Google knows. Hotjar records your mouse movements and scrolling behavior. And they keep all of this for 36 months.
Internxt Send claims "zero trackers" in its marketing, but their actual privacy policy lists Google Analytics, Facebook Pixel, and Google AdSense cookies. We left them out of the table because the contradiction makes it hard to know what is actually running.
For transparency: sto.care uses Google Analytics for basic site stats (which pages get visited, what countries traffic comes from). No Facebook Pixel, no ad networks, no heatmaps, no marketing emails.
The WeTransfer AI training story
In July 2025, WeTransfer (now owned by Italian company Bending Spoons) updated their terms of service. The new terms included a clause granting WeTransfer a "perpetual, worldwide, royalty-free license" to use uploaded content for "developing and improving the Service or new technologies, including to improve performance of machine learning models."
In plain English: anything you uploaded could be fed into AI training.
The backlash was immediate, especially from photographers and designers who had been using WeTransfer to send client work for years. WeTransfer reversed the terms within days, but the damage was done. Competing services reported 25% surges in new signups during the fallout.
The lesson: with server-side encryption, the company can do whatever they want with your files. A privacy policy is just a promise. And promises change when ownership changes. Bending Spoons bought WeTransfer in 2024 and cut 75% of the staff before the terms update.
What happens when you share a link on chat?
This one catches people off guard. You upload a file to a private service and paste the link into Slack, Discord, or Facebook Messenger. You think only the recipient sees it. Not quite.
Most chat apps generate link previews by fetching the URL from their own servers. That means Slack, Discord, Facebook, and LinkedIn all request the link before the recipient even clicks it. A 2020 study by security researchers at Mysk found that some apps downloaded entire files during preview generation. Instagram servers pulled down a 2.6 GB file sent via DM.
The good news for end-to-end encrypted services: the decryption key lives in the URL fragment (after the #), and browsers never send fragments in HTTP requests. So even if Slack's servers fetch the link, they cannot decrypt the file.
The not-so-good news: the chat platform still knows the link exists, when it was shared, and between whom. The file stays encrypted, but the metadata does not.
Where your files physically live matters
Privacy laws vary by country, and the country where your files sit determines which government can compel the service to hand them over.
- Switzerland (SwissTransfer, Tresorit): Swiss privacy law fines individual company officers, not just the company. That creates a strong personal incentive to follow the rules. Foreign government data requests face extra legal hurdles.
- EU/EEA (TransferNow, Smash, Internxt): GDPR gives you the right to access, correct, and delete your data. Fines go up to 4% of worldwide revenue.
- United States (Wormhole, file.io, sto.care via AWS): No comprehensive federal privacy law. Subject to FISA, national security letters, and the CLOUD Act, which lets US courts compel data from American companies even when the data is stored overseas.
For most people, jurisdiction is not the deciding factor. But if you are sharing something genuinely sensitive, Swiss or E2E-encrypted services give you the strongest legal and technical protection.
What "deleted" actually means
When a file sharing service says your file has been deleted, what actually happens?
Cloud providers like AWS and Google Cloud typically use cryptographic erasure: they destroy the encryption key, which makes the data on disk unreadable even though the physical bytes might linger briefly. Google Cloud switched to cryptographic erasure exclusively in late 2025.
For end-to-end encrypted services, this is even stronger. The encryption key was never on the server. Once the encrypted blob expires and gets removed, nobody can reconstruct the original file. The server never had the ability to decrypt it in the first place.
No cloud service can prove to you with 100% certainty that every copy is gone from every backup tape and CDN cache. That is a fundamental limitation of uploading anything to someone else's computer. If that is a dealbreaker, OnionShare is the only option where the file never leaves your machine.
How to pick based on what you actually need
Not every file transfer needs military-grade privacy. Here is a practical way to think about it:
- Sending a presentation to a coworker? Any reputable service works. sto.care, SwissTransfer, or WeTransfer will all get the job done. Server-side encryption is fine here.
- Sharing medical records, legal documents, or financial data? Use an end-to-end encrypted service like Wormhole or Tresorit Send. The service cannot read the file, and neither can anyone who intercepts the link without the URL fragment.
- Sharing something you genuinely need to stay private? OnionShare over Tor. No server, no company, no data retention. The tradeoff is that both you and the recipient need Tor Browser, and you need to stay online until the download finishes.
For most everyday file transfers, the biggest practical step you can take is avoiding services that track you with advertising pixels. You came here to share a file, not to feed data into ad networks.
FAQ
Can file sharing services read my files?
Only if they use server-side encryption (they hold the key). Services with end-to-end encryption like Wormhole, Tresorit Send, and OnionShare cannot read your files because the decryption key never reaches their servers.
Can I share files without creating an account?
Yes. sto.care, SwissTransfer, Wormhole, file.io, and several others let you share files without an account. Some ask for a one-time email verification. Others need nothing at all. But skipping the sign-up form does not mean your activity is invisible.
What is end-to-end encrypted file sharing?
Your file gets encrypted in your browser before it leaves your computer. The decryption key goes into the URL after the # symbol, which browsers never send to servers. The company hosting the file only sees encrypted data and cannot decrypt it.
Does WeTransfer track you?
Yes. WeTransfer uses Google Analytics, advertising cookies across multiple domains, and marketing trackers. In July 2025, they also tried to claim AI training rights on uploaded files before reversing course after public backlash.
Which file sharing service is most private?
OnionShare, because your computer is the server and no third party touches your file. For something more practical, Wormhole and Send (send.vis.ee) offer end-to-end encryption with no email required.
Is anonymous file sharing legal?
Yes. The legality depends on what you share, not whether you used an account. Sharing copyrighted material or illegal content is illegal no matter which service you use.
What data do file sharing sites collect?
It varies wildly. TransferNow uses Facebook Pixel, Google Ads, Bing Ads, and Hotjar, keeping data for 36 months. Wormhole and OnionShare collect essentially nothing. Most services fall somewhere in between. Always check the privacy policy, not the marketing page.
What happens to files after they expire?
Cloud providers typically use cryptographic erasure, destroying the encryption key so the data becomes unrecoverable. For end-to-end encrypted services, the key was never stored server-side, so the encrypted data is useless after expiry. No cloud service can guarantee every last copy is gone from all backups.